Web3 is the future. Do you know why? That’s because it is decentralized, transparent, and unstoppable.
Businesses and developers are now turning to innovative Web3 solutions to create more secure, transparent, and user-driven ecosystems. But for every Web3 project pushing boundaries, there is a hacker hiding behind the curtains, waiting to turn one overlooked issue or vulnerability into a multimillion-dollar payday.
If you had been in the space for more than five minutes, you would have seen it happen. This includes rug pulls, reentrancy attacks, flash loans, and the list keeps growing.
The truth is, investing in a Web3 project isn’t just about smart contracts and tokenomics. It is also about survival.
Thus, protecting your Web3 project from exploits isn’t just optional; it’s more important than ever. Want to know how you can do that? Here’s a blog for you!
Let’s read it together till the end!
Some Common Web3 Exploits
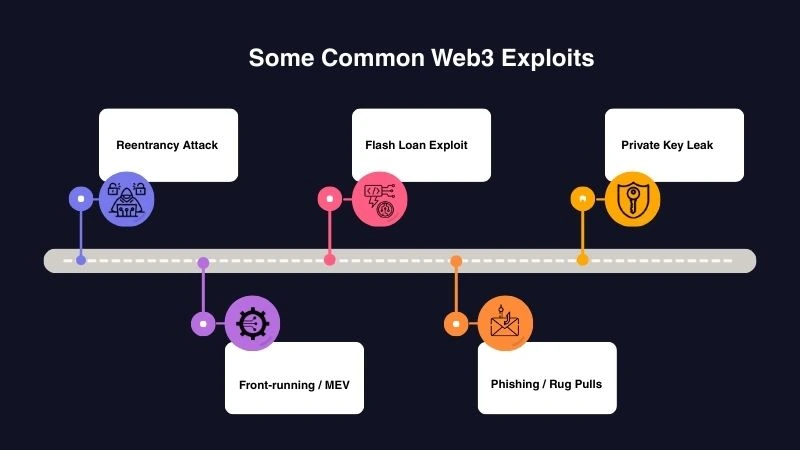
Before we talk about how to protect, let’s understand what these Web3 exploits are. Here we go!
Reentrancy Attack
A reentrancy attack occurs when a smart contract allows an external contract to call back into it before its state has been updated. This is one of the major loopholes that can let attackers withdraw funds again and again and can even manipulate the balances. It arises from poorly structured code or missing security practices.
Example: The DAO hack of 2016 exploited a reentrancy flaw. It enabled hackers to drain off approximately $60 million in Ether. This highlights how crucial it is to have well-designed contracts and to double-check everything.
Flash Loan Exploit
Flash loans are quick loans that need to be paid back in one transaction. Though designed for legitimate uses like arbitrage, attackers can misuse them to manipulate token prices, deceive protocols, or drain off funds.
Example: In 2020, the bZx protocol suffered a flash loan attack where attackers borrowed a large amount of Ether, manipulated token prices across exchanges, and profited around $350,000 in a single transaction.
Private Key Leak
Private keys play an important role in Web3 security. If a private key is compromised, the person can take control of the linked crypto wallet or smart contract, emphasizing the serious risks of key leaks. Leaks can occur from phishing, inadequate storage practices, or human mistakes.
Example: In 2021, a hacker stole $139 million by obtaining a developer’s private key for the BXH (Boy X Highspeed) decentralized cross-chain exchange. This shows how important it is to keep keys secure, use hardware wallets, and stick to the best practices for Web3 projects.
Front-running / MEV (Miner Extractable Value)
Front-running occurs when someone observes a pending transaction and executes their own transaction first to gain profits. Miner Extractable Value (MEV) is a broader concept where miners or validators reorder, include, or censor transactions for gain.
Example: On decentralized exchanges like Uniswap, bots often front-run large trades by placing their orders first, buying tokens at lower prices, and selling them for profit. This can negatively impact regular users. This phenomenon highlights the need for protocols to consider transaction ordering and fairness.
Phishing / Rug Pulls
Phishing and rug pulls are social attacks targeting users’ trust. Phishing tricks users into revealing wallet access or signing malicious transactions, while rug pulls occur when project developers abandon a project after collecting investor funds.
Example: The Squid Game token scam in 2021 promised investors rising token prices, but the developers drained the liquidity pool. This demonstrates that Web3 projects should prioritize transparency, audits, and community trust to prevent losses.
Key Tips to Protect Your Web3 Project from Exploits

Now that we know what common Web3 exploits look like, let’s talk about how to prevent them. Here we go:
Conduct Smart Contract Audits
A professional smart contract audit helps identify vulnerabilities before hackers do. Security firms review your code for common issues like reentrancy or logic flaws.
It is a crucial step before launch and after major updates. A verified audit not only strengthens your project’s defenses but also boosts transparency and investor trust in your platform.
Implement Multi-Signature Wallets
Multi-signature wallets require approvals from multiple private keys before executing any transaction. This prevents a single compromised key from draining project funds.
In addition to that, multi-sig wallets add an extra layer of governance and accountability. This ensures that all fund movements are transparent, authorized, and secure from threats.
Secure Private Keys & Use Hardware Wallets
Private keys grant full control over crypto assets, so keeping them safe is important. Hardware wallets keep your keys stored offline, which is a great way to keep them safe from hacks or malware.
It is important for you to know that saving keys in plain text or online storage is a dangerous practice. For organizations, using advanced tools like Multi-Party Computation (MPC) helps get rid of single points of failure.
Implement Best Coding Practices
You need to follow secure development standards and use reliable libraries like OpenZeppelin to avoid deploying risky code on the mainnet. Also, conduct peer reviews, write clear documentation, and test thoroughly before deployment.
Other than that, you can use automated tools such as Slither or MythX can detect hidden bugs early. A disciplined coding process ensures consistent security, scalability, and reliability across your Web3 wallets and apps.
Educate Your Community
A strong and informed community is your first line of defence. Educate users about phishing scams, fake websites, and fraudulent projects. Share verified links, security updates, and educational resources regularly.
Building awareness fosters user trust, minimizes human errors, and helps your project maintain a credible reputation in the fast-moving Web3 ecosystem.
Regularly Update & Patch
Web3 technology evolves rapidly, and outdated code can quickly become a target. Regularly update dependencies, apply patches, and follow the latest security standards.
Even small upgrades can close newly discovered vulnerabilities. A continuous improvement mindset keeps your project resilient against emerging threats and ensures your ecosystem remains reliable and secure.
The End Note
That’s it for this blog!
The Web3 world is thrilling. Every day brings new projects, tokens, and possibilities that push the boundaries of what’s possible online. But the more innovative your project is, the more it attracts attention from hackers.
That’s why security plays an important role. And our blog explains the way that can help your Web3 project from exploits.
So, if you are building in Web3, make security your best friend. Because the projects that last are the ones that stay alert, stay transparent, and stay secure.
And if you are looking for a trusted partner to guide you through it all, Coin Developer India has your back. Get in touch with us now!
FAQs
What are the most common Web3 security vulnerabilities?
Some of the most common Web3 vulnerabilities include reentrancy attacks, flash loan exploits, private key leaks, and phishing scams. These issues often arise from insecure coding, poor key management, or social engineering tactics.
How can smart contract audits prevent hacks?
Smart contract audits help detect vulnerabilities before they can be exploited. Professional auditors review the code line by line to identify bugs, logic errors, or loopholes. This step ensures that your Web3 solutions run safely and efficiently on the blockchain, protecting both project funds and user trust.
What are the best tools for Web3 security monitoring?
Some of the most trusted Web3 monitoring tools include Forta, Tenderly, OpenZeppelin Defender, and Chainalysis.
How often should a Web3 project be audited?
Ideally, a Web3 project should undergo a full smart contract audit before launch and after every major update or code change. Continuous auditing ensures that any new vulnerabilities are detected promptly. This helps your Web3 solutions stay secure and compliant as the blockchain landscape evolves.
What are the biggest Web3 hacks in history?
Some of the most significant Web3 hacks include The DAO hack (2016), Poly Network hack (2021), and Ronin Network hack (2022). These incidents resulted in hundreds of millions of dollars in losses.








